The automotive industry is undergoing disruptive change: Vehicles are becoming more efficient and intelligent thanks to the installation of electronic control systems, intelligent components, embedded systems, and API interfaces. However, along with the undeniable benefits of digitalization, there is also a dangerous downside: with each additional component that can be controlled electronically, the risk and magnitude of a potential cyber attack increases. A number of new automotive cyber security regulations are designed to protect suppliers and their customers alike. In this blog post, automotive companies can learn from which side they are at risk, how the new regulations are designed to protect them, and why getting their own cyber security audited makes sense.
CONTENT
- Why is automotive cyber security so important?
- What is the automotive industry at the center of so many attacks?
- What are the attack vectors?
- UNECE R 155 & 156: Regulations for Automotive Cyber Security
- Who do the new regulations apply to and what are their implications?
- What is a cyber security management system (CSMS) and what are its benefits?
- The best way to a CSMS: ISO 21434 and the introduction of the vehicle cyber security audit
- How can organizations prepare for a VCS audit?
- Automotive cyber security: why organizations should act now
- Successful certification with DQS
Why is automotive cyber security so important?
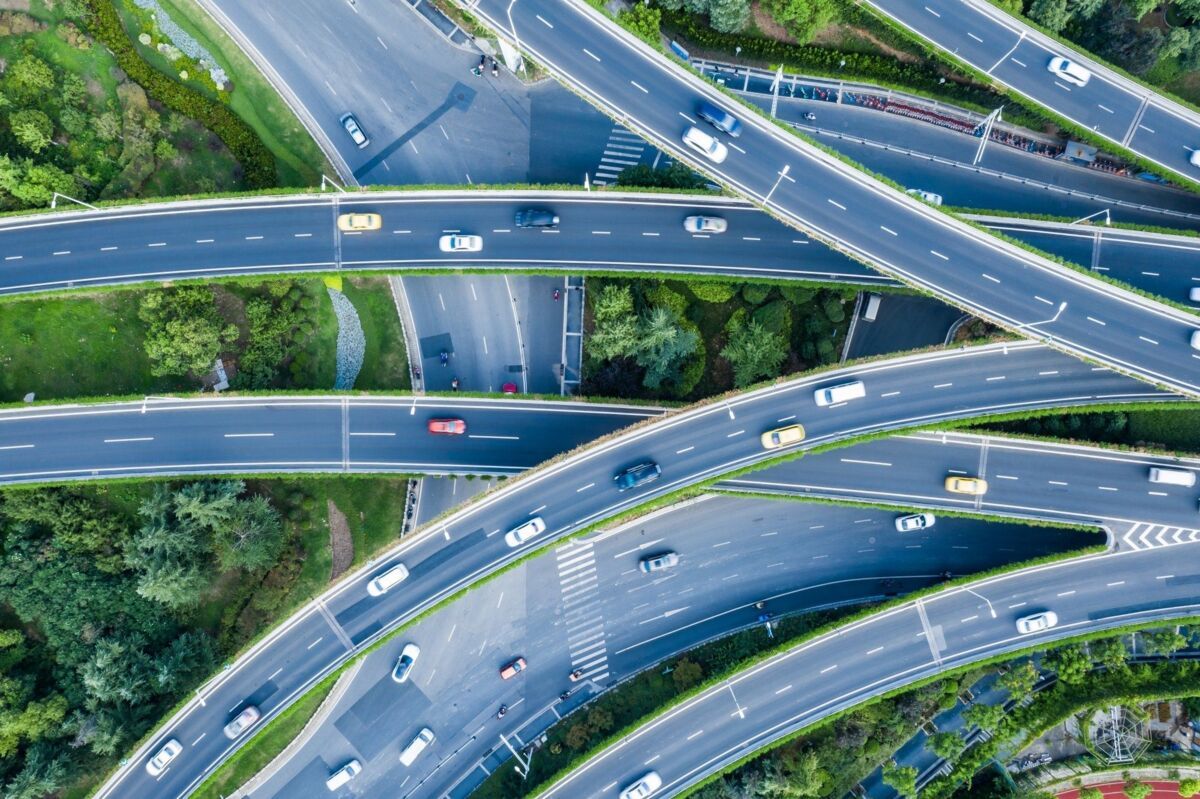
The development and design of vehicles has changed dramatically in recent years: What was once a mechanical means of transportation has long since become a computer with wheels. Where once vehicle parts such as the brake pedal and brake or the steering and front axle were physically connected, they now communicate as a system exclusively through digital controllers that send electrical signals to actuators. Almost every component in a modern vehicle is digitally networked to ensure optimal performance and driving safety. As a result, the modern smart car is always online - but the various on-board computers and assistance systems are also a growing target for cyber attacks.
A realistic and frightening scenario is the manipulation of the engine, brakes or steering, which could pose a life-threatening danger to the vehicle's occupants and other road users. The issue of autonomous driving is even more explosive: depending on how much decision-making power the electronic control systems have, (remote) intervention in their driving behavior can have fatal consequences.
Why is the automotive industry at the center of many attacks?
While the international ISO 27001 standard is the cross-industry approach to information security, the term automotive cyber security describes the security of digital systems in the automotive industry. Our motor vehicles are increasingly dependent on networked electronic systems and software applications. As a result, protecting and securing these components is becoming increasingly important - across the entire industry. This starts with the vehicle manufacturer, continues with the suppliers and engineering service providers, and extends to the software and ICT infrastructure service providers. Two new United Nations regulations, directed at manufacturers and their suppliers, are designed to ensure the security of automotive IT.
"Cyber Security Management System (CSMS) refers to a systematic, risk-based approach to establishing organizational processes, responsibilities, and governance in managing risks related to cyber threats to vehicles and protecting vehicles from cyber attacks."
Source: Official Journal of the European Union at R 155
What are the attack vectors?
A modern vehicle can be targeted by hackers in many different ways. Here are a few examples:
- Perhaps the most dangerous gateways into the vehicle system and ECUs are the connectivity features of modern vehicles, especially the wireless interfaces via Bluetooth and WLAN. In addition to the infotainment system, the proliferation of companion apps, which can be used to control critical functions, is also a significant vulnerability.
- More and more auto makers are relying on over-the-air updates to protect themselves and their customers from time-consuming recalls and expensive service visits. However, vehicles that can receive over-the-air updates are also more vulnerable to infiltration by malicious actors. OTA updates pose the highest risk for large-scale cyber attacks targeting entire model lines.
- Vehicle-to-everything (V2X) connectivity will also require more attention in the future. V2X refers to the constant communication between vehicles and entities in their environment, such as between vehicles themselves, to avoid traffic jams and accidents by comparing their locations.
- The growing influence of artificial intelligence is already evident. AI-based methods are making attackers faster and more creative. This must be countered with a robust response, such as AI-based preventive vulnerability scanning.
- Sometimes the danger is much more tangible: keyless entry systems, for example, pose a risk of vehicle theft by intercepting or spoofing signals.
ISO 27001 - the information security original
ISO/IEC 27001 is the leading international standard for the introduction of a holistic management system for information security. The ISO standard has just been revised and republished on October 25, 2022.
UNECE R 155 & 156: Regulations for Automotive Cyber Security
To address the growing threats to the automotive industry, the UN launched two important new regulations in the summer of 2020: UNECE R 155 and UNECE R 156.
- UNECE R 155 defines requirements for the protection of vehicles against cyber attacks and emphasizes the key role of a carefully implemented Cyber Security Management System (CSMS).
- UNECE R 156, on the other hand, focuses on ensuring continuous security throughout a vehicle's life cycle and mandates the implementation and operation of a standard-compliant Software Update Management System (SUMS).
Both regulations will come into force at the beginning of 2021, and compliance has only been mandatory for new vehicle types since July 2022. Finally, by July 1, 2024, the regulations will apply to all newly manufactured vehicles.
While there is no question that the new regulations are generally sound, many organizations were quick to criticize the new rules: They were too general and offered few concrete recommendations for action. So let's take a closer look at the new regulations.
UN Regulation No. 155 - Uniform provisions concerning the approval of vehicles with regard to cybersecurity and the cybersecurity management system [2021/387]. The text of the regulation can be found here.
UN Regulation No. 156 - Uniform provisions concerning the approval of motor vehicles with regard to software update and software update management system [2021/388]. The text of the regulation can be found here.
Who do the new regulations apply to and what are their implications?
The new regulations apply to all organizations that place cars and other vehicles on the market and oblige them to ensure the cyber security of their products and systems throughout the supply chain. OEMs are also responsible for their suppliers - and are now contractually obligating them to implement the new requirements.
In the recent past, several auto makers have been forced to completely discontinue some older model lines. Not because they were not successful, but because it was simply not feasible (or contractually enforceable) to guarantee software updates for the entire life cycle of these older models.
The reason: a vehicle typically has a much longer lifecycle than software applications. The ability to provide updates in 10 or more years did not seem assured for the products being phased out. Many OEMs and suppliers had not considered the costs that could arise from the new UNECE R 155 due diligence obligations in the vehicle lifecycle. The new requirements for CSMS and software updates are designed to ensure that cyber security responsibilities are contractually agreed and that the necessary skills and competencies are in place over the typical vehicle life cycle of 15 years. Organizations can obtain proof of conformity for their CSMS through a VCS audit by DQS.
What is a Cyber Security Management System (CSMS) and what are its benefits?
The goal of implementing a CSMS is to systematize cyber security in the organization and align it with established national or international standards. Key aspects for the successful implementation of a CSMS are
- The organization must have an up-to-date risk management system and defined robust processes for risk identification, risk assessment and risk mitigation of cyber threats.
- Risk management covers the entire product life cycle - from development, production and operation to disposal.
- Comprehensive monitoring of new vulnerabilities and known attacks enables rapid response to cyber attacks with targeted updates.
A CSMS offers organizations a number of benefits beyond risk mitigation and compliance: Chief among them is that it makes the organization's cyber security measurable - typically as part of an independent assessment by an authorized audit service provider. The organization knows where it stands and can prove it at any time. In addition, external audits provide unbiased openness to those aspects of cyber security that still need strengthening.
In addition, as part of this process, automotive suppliers must take an in-depth and risk-oriented approach to maintaining the vehicle's information security throughout its life cycle, thus raising awareness of cyber security across all hierarchical levels.
The best way to a CSMS: ISO 21434 and the introduction of the vehicle cyber security audit
In August 2021, the International Organization for Standardization (ISO) and the Society of Automotive Engineers (SAE) published ISO/SAE 21434, providing an internationally valid guideline for the implementation of a CSMS that organizations can use as a reference.
As expected, however, there have been varying interpretations of the standard in application. As the importance of coherent security measures is particularly high in the automotive industry with its deeply integrated supply chains, ENX promptly made improvements: with the Vehicle Cyber Security (VCS) audits, it presented a new option for proof of conformity that is more uniform and even better tailored to the requirements of the industry.
The globally standardized VCS audit is still based on the ISO 21434 standard but has been supplemented by a number of necessary extensions in close cooperation with organizations in the automotive industry. Looking to the future, the audit catalog is designed to be quickly updated as needed to respond more quickly to new developments in the automotive industry or the cyber threat landscape.
ISO/SAE 21434:2021 - Road vehicles - Cybersecurity engineering - Issue date 2021-08. The standard is available from the ISO website.
How can organizations prepare for a VCS audit?
The prerequisite for a VCS audit is a TISAX® assessment, which proves the conformity of the central ISMS with TISAX®. The ISMS ensures that fundamental rules and procedures for secure information processing are adhered to. The number of sites included in the VCS audit must be a subset of the sites included in the TISAX® assessment. In addition, a central QMS must be implemented in the organization (possible standards: IATF 16949, ISO 10007, Automotive SPICE®, ISO/IEC 330xx, ISO/IEC/IEEE 15288 or ISO/IEC/IEEE 12207).
The organization must identify which label it must provide to OEMs or other suppliers. These label requirements determine which specific requirements of the VCSA test catalog must be met:
1. VCS Development: the organization is responsible for VCS development activities up to production readiness
2. VCS Production: the organization manufactures preconfigured VCS components in a secure manner
3. VCS Operations & Maintenance: the organization monitors the secure operation of VCS components and manages security incidents, for example by developing updates and delivering them via the OEM's central fleet management system.
The VCS audit process consists of the following phases:
1. In the kickoff, the VCS lead auditor presents the process in detail and formulates his expectations for the input of the people and sites involved. In this step, the lead auditor determines the number of VCS projects in the organization and their risk assessment.
2. The organization performs a self-assessment for the central CSMS based on the ENX VCSA audit catalog and submits the result, including the referenced CSMS documents, to the lead auditor.
3. At the site where the central CSMS is maintained, the conformity of the policies and processes is verified on site based on evidence.
4. The lead auditor selects a risk-based sample from the set of VCS projects. The risks can be derived from the results of the internal project evaluation called Threat Analysis and Risk Assessment (TARA). If the sample is unusually larger than the original estimate, the DQS estimate will be adjusted to reflect the increased effort.
5. The VCS projects in the sample determine which development teams at which VCS locations are specifically included.
6. Selected development teams will be interviewed remotely with the involvement of a VCS expert to determine how the VCS project was implemented and whether the CSMS requirements were met throughout all phases of the VCS component life cycle.
Similar to TISAX®, a successfully audited VCS customer receives the above mentioned labels in the ENX database and can make the results available to interested parties (OEMs and customers). The VCS labels are valid for 3 years.
Automotive cyber security: why organizations should act now
As mentioned above, the new regulations will go into effect on July 1, 2024 for all newly manufactured vehicles. In a worst-case scenario, manufacturers that do not comply with the CSMS and software update requirements will face the risk of not receiving approval for the relevant vehicle types. Certification according to the new VCS audit, on the other hand, sends a strong signal to regulators and business partners, certifies the implementation of all safety-related aspects and ensures long-term confidence throughout the entire vehicle lifecycle.
Quality in the automotive industry
Are you looking for market access to the automotive industry or would you like to obtain it as a top supplier? Automotive manufacturers expect you to provide meaningful proof of your quality capability: a certificate according to IATF 16949.
Successful certification with DQS
DQS is your specialist for audits and certifications of management systems and processes. As a recognized audit service provider of the ENX Association, we offer you accreditations for all relevant standards in the automotive industry. With our products such as quality management according to IATF 16949 or our TISAX® assessments, we and your DQS auditors have already acquired extensive industry knowledge.
Take advantage of our experts' knowledge and get detailed information about the new automotive cyber security regulations and their impact on your organization. With more than 35 years of experience and the know-how of 2,500 auditors worldwide, we are your competent certification partner and provide answers to all questions regarding data protection and information security.

We will gladly answer your questions
What are the requirements for certification to ISO 27001, IATF 16949 or ENX VCS or a TISAX® assessment? And how much effort do you have to expect? Find out. Free of charge and without obligation.